CableBeachProposal
From OpenSimulator
| This article or section is a Proposal It does not represent the current state of OpenSim, but is an idea for future work in OpenSim. Please feel free to update this page as part of the proposal discussion. |
Contents |
Cable Beach Proposal
Motivation
Many virtual worlds are being developed independently with a wide variety of different architectures and protocols. The current generation of virtual worlds are implemented as proprietary stacks of services, where each world is not only simulating virtual space but also providing identity services, content hosting, digital rights management, instant messaging, virtual economies, social networking elements such as groups, and many other services. We believe there are shortcomings with this approach. Specifically:
- The barrier to entry for creating and running a virtual world is too high. Even with popular platforms such as OpenSim, grid administrators are taking on a monumental task of overseeing many or all of the above services when only a simple world simulation is needed.
- The all-or-nothing approach of the current protocols prevents the development of a robust virtual world ecosystem, where many specialized services are provided. Today's large stakeholders in content hosting, content delivery acceleration, identity services, and social networking have no means of entry to the virtual worlds space.
- Due to the walled garden nature of current worlds, third party services such as search and digital content creation tools have been almost entirely locked out of virtual worlds.
Vision
We envision virtual worlds modeled after the current World Wide Web, with millions of independent administrative domains. Content will be spread across millions of small, independent domains as well as aggregated on large domains supporting millions of users. A rich community of value added services and the free and open exchange of content will weave the network together, much as the Web 2.0 movement is tying the web together today. Every organization can choose what services they will run themselves, what services will be provided by third parties, and which third parties will provide services. Additionally, the content rights decisions are placed in the hands of the content hosts. With the proper authentication users are free to move assets to wherever they roam.
Data services will become as important as data hosting itself. Just as search engines and content portals have changed how we use the web, services that can plug into a common interface in asset hosting will change how we use virtual worlds. Auditing services can provide an approach to rights management and traffic analytics. Existing caching techniques and services that have been built for today's web content can be leveraged for delivery of rich virtual world content.
Overview
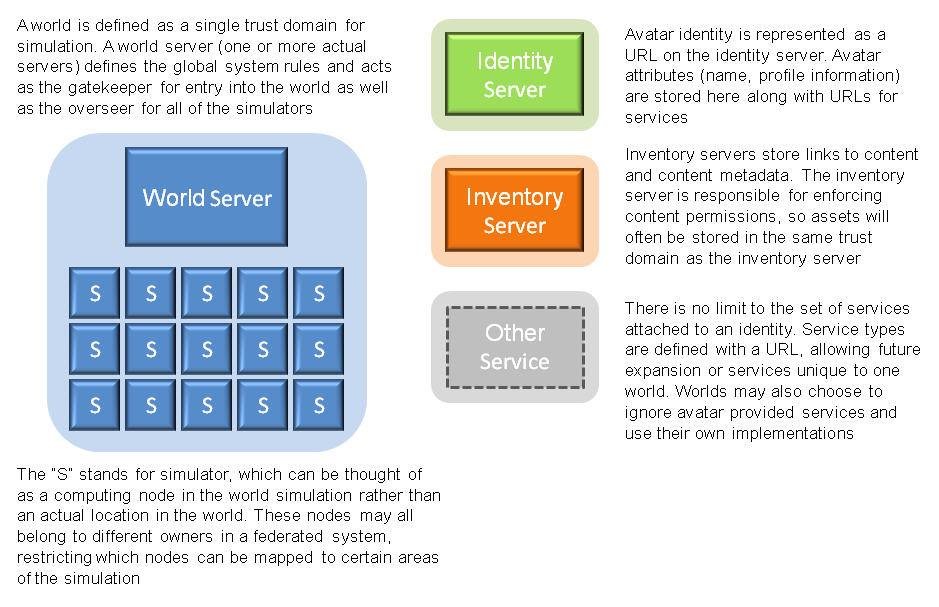
One sensible way to look at the Cable Beach architecture is by breaking it up into trust domains. Everything operating inside of a trust domain has some implicit level of trust for all of the other members of the trust domain, although that level of trust will vary depending on the purpose of the trust domain and the policy put in place for that domain.
World Domain
All of the services responsible for simulating a virtual world fall under the umbrella of the world domain. The ultimate authority of this domain is the world server, which acts as both the gatekeeper for incoming clients and oversees all of the simulation nodes in the world. The actual definition of trust is not defined by the architecture, but rather the policies of each world. In other words, the level of trust each simulator in the world has for other simulators in the world is entirely dependent on the world policies. Some worlds might choose a very tight controlled policy to facilitate the safety of online transactions, while other worlds might choose a very open membership policy. To create the notion of a trust domain across many different servers (potentially hosted by many different administrators), the world server acts as an X.509 root certificate authority. Certificates are issued to each simulator to grant world membership. These certificates can be later revoked; perhaps a member of the world has not paid their monthly dues, or has broken world policy. All clients wishing to connect to this world should connect through the world server, which will enforce global policy such as access lists.
Identity
Identity is not tied to a particular world. Instead, federated identity allows any client to attempt to login to any world. Which logins will actually be allowed are defined by policy on the world server. The closed world of fantasygameworld.com might provide its own identity server at users.fantasygameworld.com and only accept logins from identities at that domain. Another world might default to allowing logins from anywhere, but blacklist specific domains such as virtualspammers.com. This abstracts the identity and security requirements for worlds away from the architectural design and allows a wide variety of policy decisions for clients to be enforced.
In the Cable Beach architecture, identity is more than just a URL identifier. A list of attributes are attached to each identity that provide the metadata necessary to simulate the presence of an identity in a virtual world. Attribute types are defined by URLs, just as they are defined in OpenID Attribute Exchange. Each attribute stores LLSD; the format of the LLSD is specific to the attribute. As an example, an identity might have first name and last name attributes of the string type. Some attributes are references to the URL of a service, such as inventory or messaging.
When a client contacts a world server to log in, the world server contacts the identity server for the given identity. OpenID maps nicely into this process to provide proof that the client owns the supplied identity. Once authentication has completed, the identity server must contact each service the requested identity links to and request one or more capabilities on behalf of the identity. The capability is a temporary, difficult to guess URL that can be given to clients or other services to provide some level of access to a service. The confirmation of identity ownership, list of attributes for the identity, and list of services and capabilities are all returned to the world server where the login requested initiated from.
Other Services
Any number of services can be attached to an identity. Some services such as inventory might be very common across many worlds, while world-specific services such as a trophy server might apply to a very small subset of worlds or even a single world. While the first point of association with services is from identities on an identity service, world servers may also associate services with identities. For example, fantasygameworld.com may associate a trophy service with all incoming clients to track progress and achievements in that world. Inventory may be restricted to items only found in fantasygameworld.com by ignoring external inventory services and associating an internal inventory service with each identity. Future revisions may support multiple services for the same service type, such as accessing an internal and external inventory service simultaneously.
Roadmap
A roadmap has been designed to provide a migration from the current OpenSim implementation of the Second Life® protocol to a decentralized service protocol. The first step will provide some of the services in a disaggregated grid and will improve the security of existing models such as OSGrid's decentralized hosting with centralized trust. The second step will remove any assumptions about tightly coupled services and present a true decentralized virtual world service platform. Step three will remove any leftover baggage by making service authentication and authorization client-centric, and potentially enable new use cases such as multiple inventory servers or content migration.
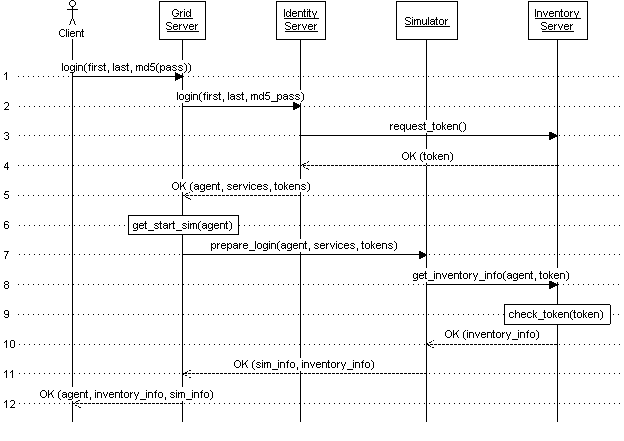
Step 1: Login With Existing LL Client
- This step is the familiar XML-RPC login initiated from the Linden Lab client, passing a first name, last name, and md5 hash of the password. What is new here is that the login is sent directly to the grid server for a grid, since identities are no longer tightly coupled to grids.
- The login is forwarded to a known identity server. Note that because the client is providing a grid server with sensitive information (md5 hash of the agent password), and it does not provide a URL for the identity server, this form of login requires the grid server and a known identity server to exist in the same trust domain.
- The identity server holds profile information for each identity, which includes a list of URLs for various services. For each service, a temporary access token is requested.
- Each service grants a temporary access token back to the identity server.
- The login request successfully returns back to the grid server with information about the agent, the list of services, and access tokens for each service.
- The grid server determines which simulator the client will start in. This may be the closest available location to a requested destination, the agent's home simulator in this grid, or the default starting location for the grid.
- The grid server contacts the starting simulator to prepare the login. Information about the agent, the list of services for the agent, and the access tokens for each service are given to the simulator. The grid server uses its certificate as a client certificate so the simulator can authenticate the request. The simulator checks the presented client certificate and confirms it as being signed by the grid server.
- The simulator contacts any services that need to be contacted before login completes. In this case, inventory information is requested from the inventory server.
- The inventory server checks the given access token and confirms that it is valid and not expired.
- The inventory server returns information about the agent's inventory.
- Information about the simulator (IP address, port, UDP circuit code) and the inventory information is sent back to the grid server along with a success response.
- Agent information, inventory information, and the simulator information are all returned to the client along with the success response.
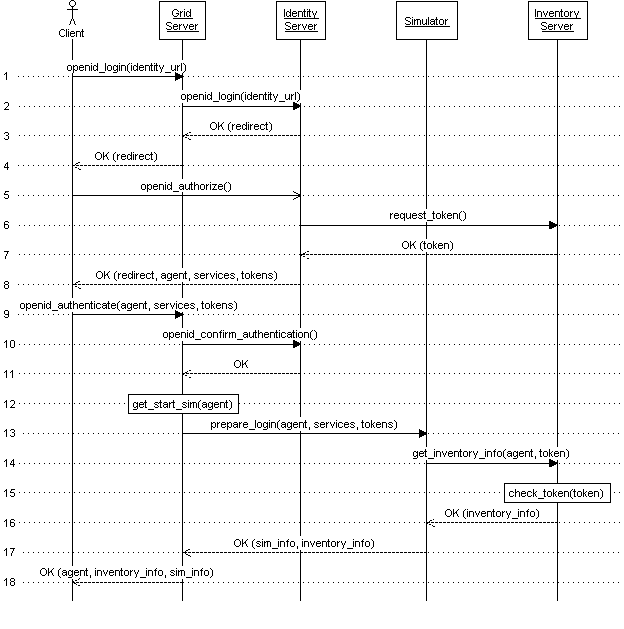
Step 2: OpenID Login With web_login_key
This is the same login flow as the first diagram, but the client passes an OpenID identity URL to the grid server instead of login credentials. An OpenID login process is initiated with the identity server where the client supplies login credentials directly to the identity server. This removes the restriction that the grid server and identity server must be in the same trust domain. The list of services and tokens are carried in the OpenID response, defined as a new namespace of data.
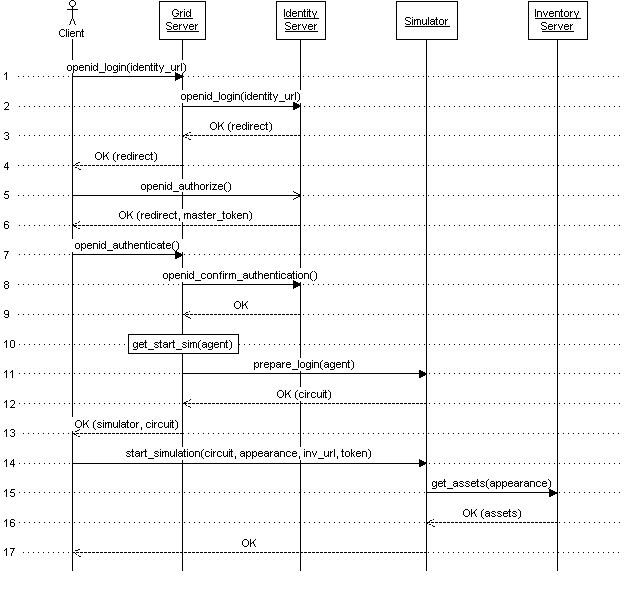
Step 3: Client-Centric World
[TODO]
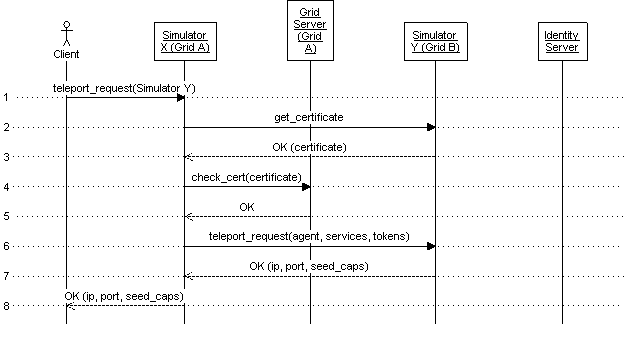
Use Cases
Several common virtual world operations are presented below. Teleporting between two regions in the same trust domain or between domains that have shared trust, teleporting between two untrusted domains, content publishing from digital content creation tools, and content migration between untrusted domains. [TODO]